IT Articles
IT Articles
IT Articles

What is Dynamic Quest Quickpass? Dynamic Quest Quickpass is an advanced end-user identity verification tool designed to enhance security by ensuring that only authorized users can access and make changes to your systems. This solution also simplifies password resets, providing a secure and efficient way for users to manage their credentials. How does Quickpass enhance security? Quickpass uses multi-factor and biometric authentication to verify the identity of users before allowing any changes to their accounts. This prevents unauthorized access and ensures that only verified individuals can reset passwords or access sensitive information. What authentication…

Enhance Security with Advanced Identity Verification Dynamic Quest provides robust security measures for our clients. Our new Quickpass solution prioritizes end-user identity verification, ensuring all password reset actions are authenticated and secure. Quickpass seamlessly integrates with your existing Change Request processes, providing an added layer of security without disruption. Key Benefits Advanced Security: Quickpass uses multi-factor and biometric authentication to confirm user identities, safeguarding against unauthorized access. Easy Identity Verification: Users can verify their identities through a secure, intuitive mobile app, significantly reducing the risk of fraud and identity theft. Convenient and Efficient: By…

In the rapidly evolving landscape of healthcare, the role of information technology (IT) and cybersecurity has become increasingly critical. From electronic health records (EHRs) to telemedicine, technology has transformed the way healthcare is delivered, improving patient outcomes, and streamlining operations. However, this digital transformation has also brought new challenges, particularly in the realm of cybersecurity. Cyberattacks targeting healthcare organizations have been on the rise in recent years, with hackers targeting sensitive patient data for financial gain. These attacks not only compromise patient privacy but also disrupt healthcare operations, leading to delays in patient care…
Effective September 1, 2023, the NCUA will require all federally insured credit unions to notify the NCUA as soon as possible, within 72 hours after a reportable cyber incident has occurred. “Each of us in the financial system has an obligation to protect our nation’s economic and financial infrastructure. And, credit unions must be included in conversations about critical infrastructure, as a whole. This final rule will facilitate such dialogue,” Chairman Todd M. Harper said. “Through these high-level early warning notifications, the NCUA will be able to work with other agencies and the private…

When using mobile devices to accomplish work tasks, consider implementing the following five overlooked security measures. Implement a mobile device policy. This is particularly important if your employees are using their own personal devices to access company e-mail and data. If that employee leaves, are you allowed to erase company data from their phone? If their phone is lost or stolen, are you permitted to remotely wipe the device – which would delete all of that employee’s photos, videos, texts, etc. – to ensure YOUR clients’ information isn’t compromised? Further, if the data in…

Firewalls are a network security device that when properly implemented will monitor all incoming and outgoing network traffic and will allow or deny data packets to enter your network based on your organization’s predetermined set of security rules. A firewall will establish a barrier between your internal network and external traffic sources. This critical form of security blocks malicious traffic, viruses, and potential hacking attempts. What Does a Firewall Do? Firewalls use predetermined security rules to analyze incoming traffic and will filter traffic from any suspicious or unsecured sources. The firewall acts as a…

A large-scale ransomware attack led the Colonial Pipeline to shut down its 5,500-mile gasoline pipeline. The pipeline is one of the largest conduits for gasoline in the country; it funnels nearly half of the gasoline used by the entire East Coast. This hack illuminates the reality that no industry, business, or organization is safe from ransomware attacks. What do we know about the cyberattack? Colonial Pipeline’s operator suffered what is believed to be one of the largest cyber attacks on the oil infrastructure in United States’ history. Ransomware attacks are performed when hackers take…

Did you know 91% of all data breaches begin with a phishing email? Phished and spoofed email messages are designed to trick you into clicking on a malicious link or attachment or revealing private information and passwords. The messages appear to be from known senders. Senders can spoof their email address to trick you into thinking the email was sent from someone you know or a brand or vendor you commonly work with. Phishing emails often bypass the spam filter because the body of the message does not contain malicious software and the sending…

Cybersecurity continues to occupy a prominent spot in companies’ priority lists. As such, companies commit substantial amounts of money to bolster cyber defenses. Norton’s 2019 data breach report revealed that bad actors breached 4.1 billion records in the first half of the year. Breaches can lead to significant reputational damage and financial losses. Hence, information security is a critical concern for organizations irrespective of whether they outsource IT functions or handle them internally. Thankfully, organizations can mitigate the risks by hiring a managed IT service provider with a SOC 2 Type 1 and Type…

In the early 20th century, if a crook wanted money, they’d rob a bank or steal a woman’s purse on the street. Real masterminds might devise an elaborate heist to hold up a Brink’s truck or befriend a millionaire, then make off with their riches. Today, these crooks look much different. That’s because an increasing number of them are not out on the street taking gold, jewelry, and cash. They’re sitting behind desks, somewhere in an unknown room where they will probably never be found, hacking your data. Why data? If you didn’t realize…

To defend against the devastation of cyberattacks, small- to medium-sized businesses must deploy a strategy that includes three critial components. If your cybersecurity is one-dimensional, it’s not cybersecurity. Threats to your data come from every direction, all the time. When companies devise brilliant new cyber-defenses, hackers come up with new cyber-weapons in about 3 minutes. They are endlessly innovative. Effective cyber-security must address every tool and technique in the hacker toolbox. 60% of SMBs fail within 6 months of a cyberattack. Most businesses underestimate their risk, with 82% of owners claiming they are not…
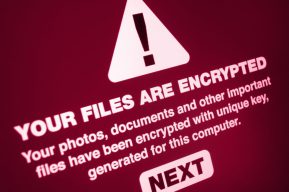
What would happen if all the files in your healthcare system were suddenly inaccessible? This might sound like an unlikely scenario, but it’s really not; a ransomware attack can hold your sensitive files hostage indefinitely. And healthcare organizations are extremely vulnerable to these types of malware attacks. Last year, estimated losses from ransomware in healthcare totaled a staggering $25 billion, and every year, these attacks affect more than 4 million patient records. You need to invest in good ransomware protection in order to comply with HIPAA regulations and safeguard patient data. Here’s everything you…




